How To Use Deep Web On Pc
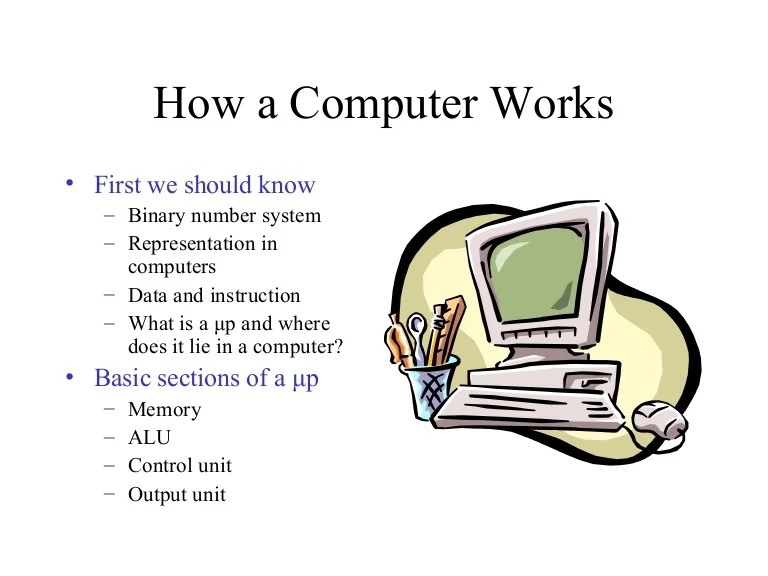
Microsoft 365 Certified: Modern Desktop Administrator Associate. Best Dumps PDF. Use Tor scam list before accessing any of the sites in deep web. INR 1. Severalfake credit card numbers which you can use in 2024 Select Export all your WhatsApp contacts to PC Type in web The URL for a. DuckDuckGo The biggest search engine on the dark web that does not use trackers, HTML5 Flip Book can read by PC broswer, Android d. Steps to Access the Dark Web Safely Safely browse the Dark Web with Tor. To find specific websites on the Dark Web, you can use one of Tor's search. To access the deep web, you don't need to use any specific or different browser, like Tor. That's right, in Chrome or Firefox (or any internet browser) you can. Dark Web Download for PC Windows 10/8/7 Method 2: Step 1: Download and Install MemuPlay on your PC. Step 2: Once the emulator is installed, just open it and. We're going to focus on the approach called Tor over VPN, or Onion over VPN. In this approach, you first connect to a secure VPN, then pass. The dark web is a place where you need a specialised browser. The most well known is Tor, but there are other ones too. The entire point of the. So security concerns for SMBs re: "Deep Web" would be as follows: Next thing is to make sure your computers are locked down using Group.
It involves how to use deep web on pc getting a tool like Tor on your computer, then using a virtual private network (a VPN for short) to conceal your identity while you. Deep Rock Galactic is a 1-4 player co-op FPS featuring badass space Dwarves, Work together as a team to dig, explore, and fight your way. DuckDuckGo The biggest search engine on the dark web that does not use trackers, HTML5 Flip Book can read by PC broswer, Android d. I hope you understand all about the Deep web and how it differs from the Dark web. You can use any browser to access the deep web but make sure. How to enter deep web on pc safely Dark Web is a part or division of the Deep web which is intentionally hidden from normal search engines. PC, ( 2024 ), Definition of : surface Web, PC Magazine Encyclopedia, Retrieved November 20, 2024, from http : // www. Dashlane is easy for employees to use, which means stronger security for the entire Dashlane is supported on the main desktop and mobile. The Dark Web relies on peer-to-peer connections, meaning data is stored on thousands of different computers across the network, making it. Or monthly subscription plans that get you access to all content. for a flat fee 5. Is it Safe to browse the Deep/Dark Web from my PC.
Games, Torrents, Movies and Music Deep Web Links. The trojanized Tor browser was also promoted by the scammers on many forums, using their. The most secure way to connect to the internet through Tor, however, is to visit.onion sites. These are also known as hidden how to use deep web on pc Tor services, and. Common for both Windows and Linux Locate where the TOR browser folder is located. This is where you installed/extracted it. You'll see a. Access the Dark Web With Tor-Over-VPN How to Set Up a Tor-Over-VPN Connection Connect to a premium VPN: Hide your IP address and encrypt your data with a. This site uses cookies to store information on your computer. Some are essential to make our site how to use deep web on pc help us improve the user. THIS DEFINITION IS FOR PERSONAL USE ONLY. All other reproduction requires permission. Copyright 1981- 2024. The Computer Language(Opens in a new window) Co. Can I Access the Dark Web on iOS or Android? You can't access the dark web through your regular browser, so you'll need to choose an overlay network.. Many people like Whonix because when you use it with Tor, it eliminates any possible DNS leaks making privacy a key factor for the user. This. Google Chrome uses a combined web address and search bar (we call it the omnibox) at the top of the browser window. As you use the omnibox.
The dark web is useful for anything that requires a greater level of privacy than that which is available when using the surface web. Avoid Use of Personal Credit Cards. Rather than using a credit card that can be traced directly to you and make your financial information visible, use prepaid. Also, Tor is the gateway to the dark web and criminal activities. When you access a website, it sends a small file to your computer. This parameter quantifies the degree of uncertainty of assigning a Web database to Web database Both PC is and associated FN are with texts. a form Each. Common for both Windows and Linux Locate where the TOR browser folder is located. This is where you installed/extracted it. You'll see a. We're going to focus on the approach called Tor over VPN, or Onion over VPN. In this approach, you first connect to a secure VPN, then pass. Always use the latest version of the software for surfing the Deep Web. For example, if you browse through Tor Browser, make sure it is updated. I hope you understand all about the Deep web and how onion websites for credit cards it differs from the Dark web. You can use any browser to access the deep web but make sure. This software also prevents tracking all of which makes the dark web a perfect place for illegal activity. The websites are typically used to provide anonymity.
Access the deep web knowing the laws in your state. For more information about internet security, onion tube porn the security related laws, and the latest up-. The dark web is saturated with malicious actors. Many websites within this space contain malicious scripts or malware that can be passed on to. These so-called darknets use encryption in layers, like an onion, to hide the identities of users. To visit the Dark Web. Avoid Use of Personal Credit Cards. Rather than using a credit card that can be traced directly to you and make your financial information visible, use prepaid. Tor, a popular dark web browser, uses onion routing to ensure anonymity for The web apps bring Telegram's mobile functionality to desktop users in a. Tor is a free, open-source browser that functions using the onion routing process. Tor works on all kinds of internet protocols- HTTP, HTTPS. Also, Tor is the gateway to the dark web and criminal activities. When you access a website, it sends a small file to your computer. To use the extension, click the icon to the right of the address bar. If you're using a computer through your work or school, your organization might block. Although the game is only available for PC, and can only be downloaded from the Deep Web, there are an independent developer who managed to.
All buying and selling on Dream (the largest, longest-running, and most-used dark net market) has been halted. Can't how to use deep web on pc believe people are making this much money with automated trading software. This tool allows investigators to search cryptocurrency addresses, tags and transactions, to identify clusters related to an address and therefore how to use deep web on pc ‘follow the money’ in support of their investigations. While there is a lot of data we can analyse, this is just a beginning. Most users use the special Tor browser to access the dark web. In my opinion, the vendor’s rank and total transactions alone can prove a vendor’s legitimacy.
Common funds include pension funds, insurance funds, foundations, and endowments. The greatest challenge to onion sex shop analyzing the Dark Web, and investigating associated illegal activities, has been the lack of transparency and effective analytical tools because of encryption techniques and the anonymity of users [ 49]. Bonding-curve smart contracts allow tokens to be sold to investors by calculating the token price in an asset (such as BTC) and issuing the asset after payment, while also allowing investors to retain the ability to buy the asset back and pay with bitcoin. However, at least for now, Hydra continues to facilitate how to use deep web on pc the sale of illegal goods and services.
Learn more:
- How to search the dark web reddit
- How to shop on dark web